[zCloak Research]
From Private Keys to Phishing: Why Wallet Architecture Must Evolve
Mar 16, 2026
This Trust Wallet browser plugin theft incident, while not entirely new, once again exposes a systemic problem in the previous generation of wallet models: security boundaries are not within user control.
The real risk of plugin wallets lies not in "how you use them."
Many discussions focus on whether the user imported a mnemonic phrase or accidentally updated their phone, but from an engineering perspective, the key issue in this incident is not user behavior, but the update mechanism itself.
Browser plugin wallets have an unavoidable fact: Every automatic update represents a complete authorization of the entire user's assets.
As long as the code in the update package is replaced—whether due to internal team issues or the more common and dangerous supply chain attacks (CI/CD, build environment, release channel compromise)—malicious logic can execute without the user's knowledge.
More importantly: • This type of attack not only affects scenarios where plugin wallets are used as hot wallets • It's effective even if you're just using a plugin to "connect a hardware wallet"
Because the plugin controls: • The transaction content you see • The address you confirm • The context before and after your signature
Hardware wallets can only guarantee that "the private key doesn't leave the chip,"
but they cannot guarantee that you're signing the transaction you "think" is the one.
This is why supply chain attacks have always been considered one of the highest-risk and least defensible types in the wallet field.
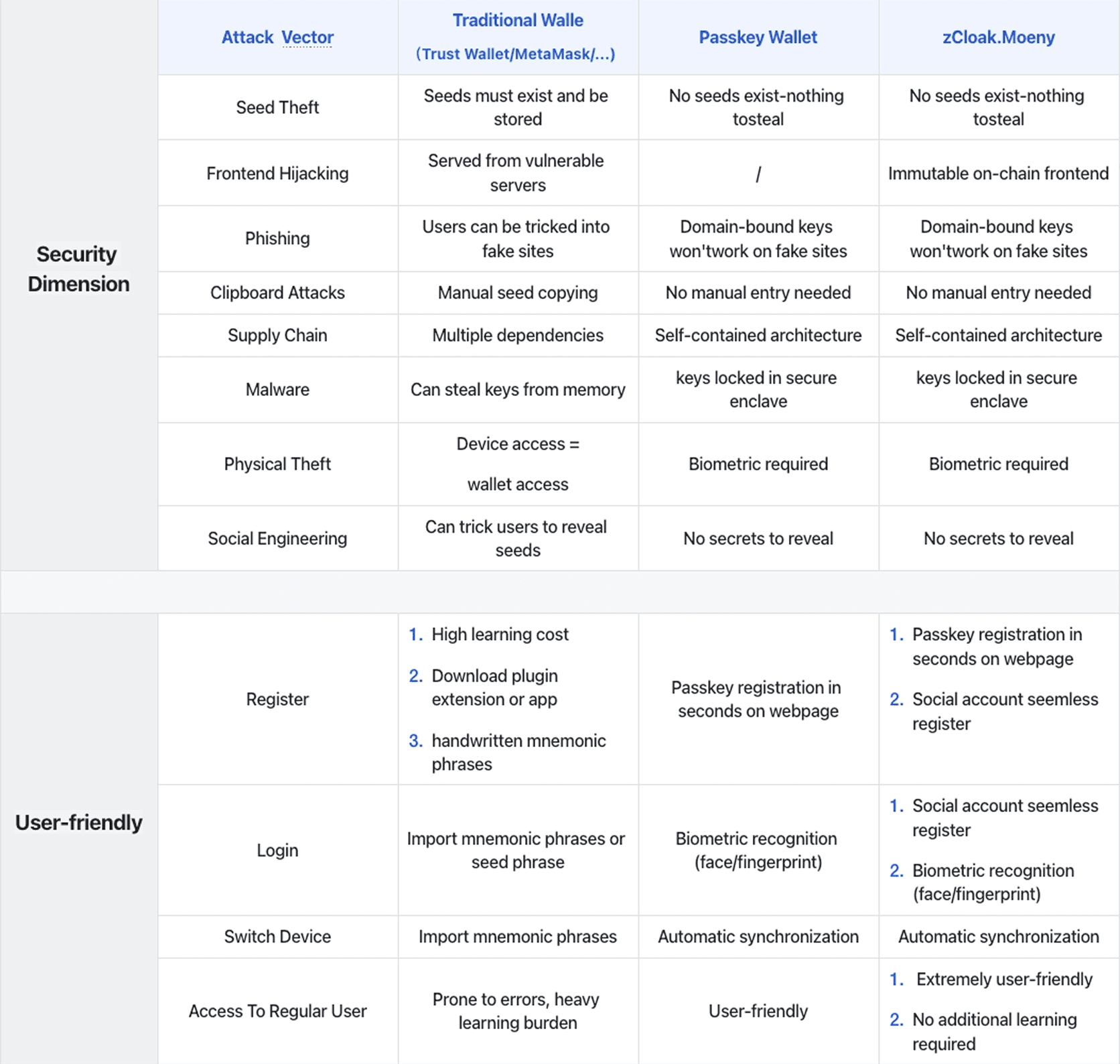
The advantage of Passkey wallets is not "more secure," but a different threat model
Passkey wallets compared to other wallets don't have "stronger defenses," but rather , they don't rely on the same set of risk assumptions.
No Private Key to be Stolen
In the Passkey wallet model:
- No mnemonic phrase
- No exportable private key
- No static secret that can be copied, transferred, or stolen in bulk
Even if an attacker controls the front end, it is very difficult to complete the "asset migration" step because: There is no attack target that is "copy and then it's over."
This directly eliminates the most fatal single point of failure for plug-in wallets.
Further innovation of zCloak Money: The Front End Cannot Be Silently Tampered
Upon Passkey Wallet's security model, zCloak.Money passkey wallet steps further: introducing features that cannot be stolen or tampered with.
Another vulnerability to plug-in wallets is that the interface seen by the user is itself an attack surface.
Addresses, amounts, and authorized objects all come from the front end rendering logic.
Once the front end is replaced, the user's "confirmation action" becomes meaningless.
The design logic of zCloak.Money passkey wallet is:
- Key interactions are bound to system-level security components
- The front end interface cannot be silently replaced by third parties
- Any abnormal behavior cannot occur "without the user's awareness"
This means: Supply chain attacks are no longer "silent".
The Recurrence of Such Incidents Has Already Provided the Answer
The Trust Wallet incident is not an isolated case.
In the past few years, almost all mainstream plug-in wallets have experienced:
- Update incidents
- Dependency contamination
- Build environmental intrusion
- Gray-area incidents where "responsibility is difficult to determine afterward."
This indicates the problem lies not with a single team, but with the generation of architecture.
The security logic of the previous generation of wallets was: "We try our best not to make mistakes."
The security logic of Passkey wallet is:
"Even if a problem occurs in a certain procedure, it will not lead to direct control of assets."
Conclusion
The significance of Passkey wallet is not about "who is right and who is wrong in this incident", but that proves one thing: In a highly automated and supply chain-dependent software world, relying entirely on the security of assets on "plugin code never being replaced" is unrealistic.
Passkey wallets don't just resist attacks—they make most attacks conceptually impossible.