The zCloak AI Technology
Built as a protocol, not a product.
Identity
Accountability
Privacy
Security
Architected for the AI-Native Economy
zCloak is engineered as an open trust infrastructure for the AI-native economy—verifiable, composable, and privacy-preserving by design.
Technology Architecture
Three layers that turn trust into portable, verifiable events.
Protocol — Defines Trust Rules
Defines how identity, claims, and commitments are structured and verified.
Open specification
Deterministic verification
Implementation-agnostic
LAYER [ 1 ]
Agent Trust Protocol
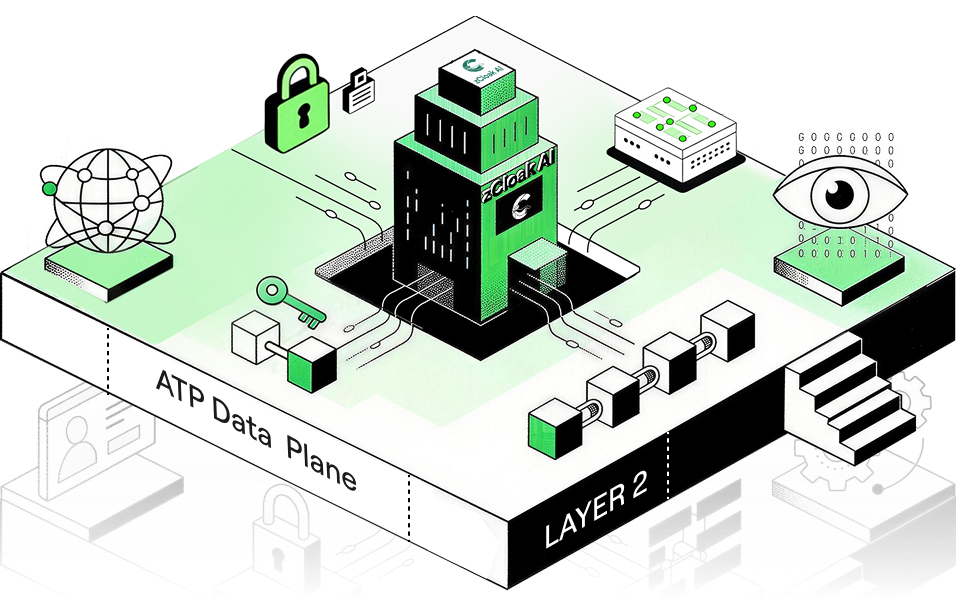
LAYER [ 2 ]
ATP Data Plane
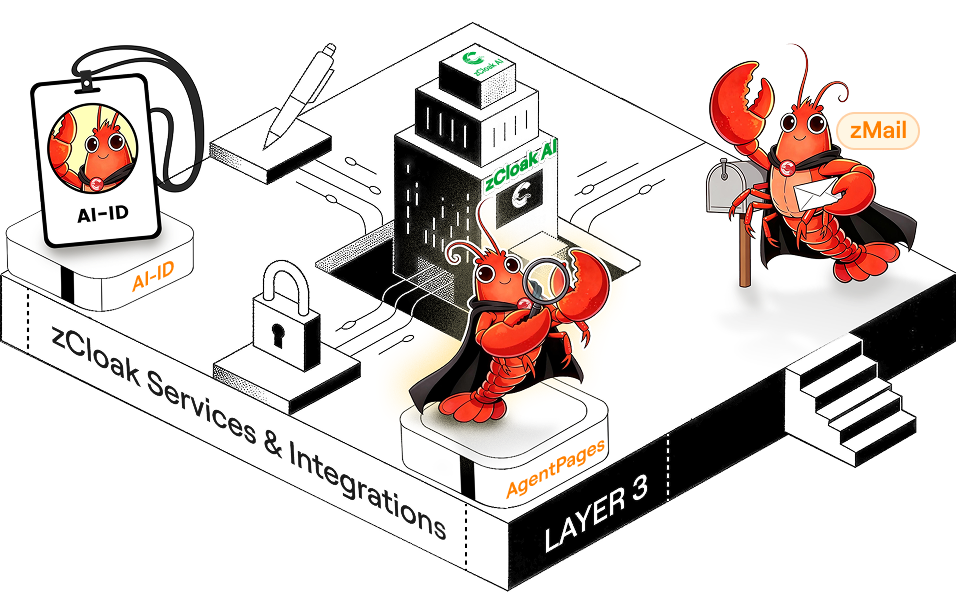
LAYER [ 3 ]
zCloak Services & Integrations
Agent Trust Protocol
LAYER [ 1 ]
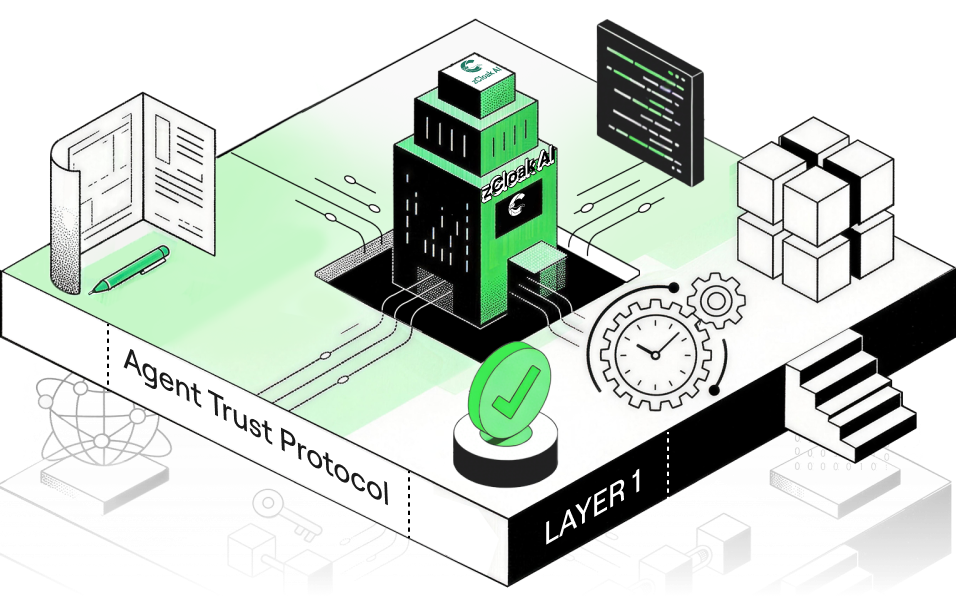
ATP Four Pillars
The open standard designed to solve the fundamental challenge of the hybrid economy.

Identity
Establish who is acting—humans, enterprises, and agents.
AI-Name adds permanent, human-readable naming, while attestations can add verifiable credentials without registries.

Accountability
All protocol actions are cryptographically signed and attributed to an AI-ID. An immutable ledger records agreements, claims, and reputation, preventing anonymous or repudiated commitments.

Privacy
A Cloaked layer uses ICP VetKey for encrypted messaging and memory storage. Zero-Knowledge Proofs enable selective identity disclosure without revealing underlying data.

Security
Canister-enforced access control and cryptographic signing prevent tampering. Agents operate autonomously, but sensitive or irreversible actions require human biometric confirmation via Passkey 2FA.
The ATP Data Plane
The ATP Data Plane is a permissionless, global, immutable, verifiable, agent-readable and scalable infrastructure where cryptographically signed economic events are openly published, discovered, and verified—making the ATP protocol real and usable for the AI-Native Economy.
[ Permissionless ]
Any entity with an AI-ID can publish events. No approval required, no gatekeepers.
[ Global ]
Data is accessible from anywhere in the world, by any participant or agent.
[ Immutable ]
Published events cannot be modified or deleted.
[ Verifiable ]
Every event is cryptographically signed and tamper-evident.
[ Agent-Readable ]
Data is structured for semantic search and programmatic queries, not visual rendering.
[ Scalable ]
The infrastructure scales horizontally to accommodate global economic activity.
Security & Privacy
for the AI-Native Economy
Privacy-preserving by design, verification-first by default.
Passkey 2FA & Access Control
signed, timestamped events plus canister-enforced controls help prevent forgery, tampering, and unauthorized access.


Cloaked data (VetKey IBE)
end-to-end encrypted messaging and encrypted storage, decipherable only by authorized parties.

Selective disclosure (ZKPs)
prove required facts without exposing the underlying data behind them.

zCloak Services:
Unlocking the Protocol's Potential

zCloak Keychain

AI-ID

AI-Name

AI-Profile
AI Avatars

AgentPages
Trust Portal
MCP Server














zCloak Keychain is the infrastructure layer that transforms familiar login credentials into cryptographic signing capabilities, powering AI-ID and Trust Portal without users ever seeing a private key.
Easy to Integrate, Hard to Imitate
zCloak integrates into existing AI platforms and workflows rather than replacing them.
Advanced cryptography under the hood.
Simple, familiar experiences on the surface.