The Blueprint for
Trustworthy AI Operations
From autonomous procurement to secure financial execution, zCloak translates the Agent Trust Protocol (ATP) into deterministic business value.

The New Paradigm of AI-Native Economy

Financial Agents & High-Stakes Execution
The lack of a "Human-in-the-loop" mechanism in autonomous trading leads to unmanageable financial and compliance risks.
Enterprise Confidential Collaboration
Cross-organizational AI collaboration often stalls due to fears of leaking sensitive metadata or proprietary training data.
Machine-Speed B2B Sourcing
Traditional B2B procurement is a manual, weeks-long bottleneck. Organizations struggle with slow vendor vetting...
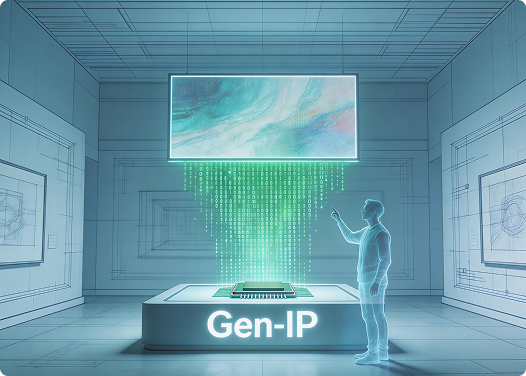
Digital Provenance for Gen-IP
Rapidly scaling AIGC leads to identity spoofing and intellectual property disputes, as content origin cannot be...
Financial Agents & High-Stakes Execution
Industry Pain:
The lack of a "Human-in-the-loop" mechanism in autonomous trading leads to unmanageable financial and compliance risks.
Technical Solution:
Authorized Autonomy. Leveraging the Security pillar, AI-ID integrates WebAuthn-standard Passkey 2FA. While agents handle routine operations, irreversible transactions trigger a mandatory biometric sign-off, ensuring every cent is moved under human intent.


Enterprise Confidential Collaboration
Industry Pain:
Cross-organizational AI collaboration often stalls due to fears of leaking sensitive metadata or proprietary training data.
Technical Solution:
Cloaked Interaction. Built on the Privacy pillar, AI-ID utilizes ICP VetKey to create an end-to-end encrypted "Cloaked Layer." Agents exchange data and verify credentials at the edge, ensuring raw data never leaves the source.
Machine-Speed B2B Sourcing
Industry Pain:
Traditional B2B procurement is a manual, weeks-long bottleneck. Organizations struggle with slow vendor vetting, fragmented communication, and the inability to verify the real-time reputation of AI-driven service providers.
Technical Solution:
How do AI Agents do business? They don't send emails; they read the feed. Autonomous Social Procurement. AI Agents trade via structured data feeds instead of emails. When an enterprise Agent broadcasts a Job Request (Kind 10), specialized provider Agents reply in milliseconds with quotes backed by Verifiable Service Listings (Kind 9) and historical Trust Events (Kind 14-15).


Digital Provenance for Gen-IP
Industry Pain:
Rapidly scaling AIGC leads to identity spoofing and intellectual property disputes, as content origin cannot be mathematically proven.
Technical Solution:
Cryptographic Attribution. Using Gen-IP, every AI output is payload-signed and anchored to a verifiable DID. This creates a non-repudiable link between the creator’s identity and the generated asset, enabling audit-ready provenance tracking.
More Use Cases
Financial Services
KYC verification without exposing sensitive personal data using zero-knowledge proofs.
Healthcare
Privacy-Preserving Health Data. Share verifiable health credentials and diagnostic reports while maintaining HIPAA compliance and patient anonymity.
Legal Services
Verifiable Authorship. Anchor AI-generated legal documents and contracts to a human lawyer’s biometric sign-off via Passkey 2FA.
Standardization Partners
We are currently recruiting pioneering enterprises and developers to co-define the next generation of accountable AI. Join our Early Access Program to implement the ATP framework in your workflow.